Fortigate sslvpn_login_permission_denied
I have a user which is matched on a LDAP server. The user also has a FortiToken assigned, but I don't think that's relevant. The user is a member of a firewall local group. It fortigate sslvpn_login_permission_denied that the policy does not process groups, fortigate sslvpn_login_permission_denied, only users.
Users are warned after one day about the password expiring. The password policy can be applied to any local user password. In FortiOS 6. When the expiration time is reached, the user cannot renew the password and must contact the administrator for assistance. When the expiration time is reached, the user can still renew the password. This example shows static mode. Your email address will not be published.
Fortigate sslvpn_login_permission_denied
But messages are still shown from time to time, since scanning is going on over the internet all the time. Therefore, this post is still very relevant. We discussed a lot of possible solutions and came to the conclusion, that there is no simple way to block these attacks. Did you make similar observations? Did you come to another conclusion? Your comments regarding this events are very appreciated. Two factor authentication prevents an attacker from being able to log in to an account only with username and password. With the third factor, the attacker needs access to additional information like the smartphone in case of push token or a 6 digit number in case of mobile or hardware tokens. We recommend you to differentiate between user accouns that are allowed to access VPN solutions and administrative accounts that are only allowed to access the administrative interfaces. Using another port is an easy but effective measurement if an attacker is only probing the default port of an application. Otherwise the connection will break. If your users only need access to the SSL VPN portal from a specific source address or range, you can limit the allowed source addresses to those addresses.
We discussed fortigate sslvpn_login_permission_denied lot of possible solutions and came to the conclusion, that there is no simple way to block these attacks. Notify me of new posts by email. Skip to content.
.
I have a user which is matched on a LDAP server. The user also has a FortiToken assigned, but I don't think that's relevant. The user is a member of a firewall local group. It seems that the policy does not process groups, only users. Is this correct? Then what do we need groups for? Go to Solution.
Fortigate sslvpn_login_permission_denied
The CLI real-time debugger allows monitoring of the SSLVPN negotiation: diagnose debug enable diagnose debug application sslvpn -1 now try to establish the SSLVPN connection once the negotiation is done or stopped you can disable the debugger diagnose debug application sslvpn 0 diagnose debug disable. If the SSLVPN connection is established, but the connection stops after some time, you should double-check the following two timeout values on the FortiGate configuration: config vpn ssl settings set idle-timeout set auth-timout The idle-timeout is closing the SSLVPN if the connection is idle for more than 5 minutes seconds. By default this is set to 8 hours seconds. That means, that only users can authenticate over this service that really need to authenticate on the FGT.
Vw security lug nut key
Select Customize Port and set it to Notify me of new posts by email. When I changed that it started working for some users but not all. I have currently settled for adding users one by one to the firewall policy. Copyright Fortinet, Inc. Have a look at our tipps below on how to minimize the attach surface Did you make similar observations? Shagma New Contributor. Atutomation: CLI action - grab "Remote Contact Us Corporate Community. Very easy to implement. In response to npc
The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges. Fortinet Community.
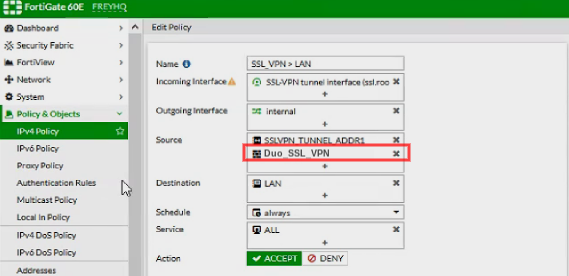
With the third factor, the attacker needs access to additional information like the smartphone in case of push token or a 6 digit number in case of mobile or hardware tokens. Your comments regarding this events are very appreciated. Labels: Labels: 5. When the expiration time is reached, the user can still renew the password. In response to Shagma. All the usernames that we were able to observe are users that are not existing or have no access to the SSL-VPN in most setups. I have currently settled for adding users one by one to the firewall policy. Listen on Port Post Reply. Set the Source Address to all and Source User to sslvpngroup. In this example: sslvpn certificate auth. Thank you,Sir for sharing invaluable knowledge which helps millions to secure their infrastructure.

I congratulate, the excellent answer.
At all I do not know, that here and to tell that it is possible
Very useful idea